What is the Dark Web? How to Stay Safe Online

The internet is immense and complicated, and we can look at it as having three layers: Surface Web, Deep Web, and Dark Web. Whereas most users do their questing and browsing on the Surface Web, including sites such as Google, Facebook, or YouTube, there exists yet another hidden part of the internet that is so-called Dark Web. It consists of internet sites which traditional search engines cannot index and which can be accessed only using specialized tools such as the Tor browser.
The Dark Web is assumed to be a haven for many illegal trades of all kinds. But then again, it serves as an avenue for privacy-seeking citizens, journalists, and whistleblowers alike. It may prove very risky to traverse this hidden part of the internet without proper precautions. In this guide you shall come across Dark Web, its nature of functioning, legitimate and illegal use, and most importantly your safe online navigation.
Understanding the Layers of Internet
To properly appreciate the Dark Web, it is crucial to highlight the three main layers of the internet.
1. Surface Web
The Surface Web is that unrestricted part of the internet that is publicly accessible anytime and is indexed by sufficient search engines, namely Google, Bing, Yahoo, etc. Examples would include:
News websites: CNN, BBC
Social media platforms: Facebook, Twitter
E-commerce: Amazon, eBay
This constitutes only 4-10% of the entire internet.
2. Deep Web
Deep web consists of web pages which may have been created and uploaded to the World Wide Web but which remain unindexed by search engines and for which the user requires certain credentials to access them. These include:
Email accounts (Gmail, Outlook)
Online banking portals
Private company databases
Academic research sites
These make up about 90-96% of the internet and are not inherently dangerous.
3. Dark Web
The Dark Web is the smallest part of the Deep Web and is accessible only through the use of special software such as Tor (The Onion Router) or I2P (Invisible Internet Project). It is purposely hidden and allows anonymity to users and owners of websites. Many legitimate uses lie behind the Dark Web, yet it proliferates with many illegal activities: black markets, hacking forums, and data leaks.
How The Dark Web Works?
The Dark Web operates like an anonymous pathway and gets access through a browser such as Chrome or Firefox at the front surface of the web contradicting the leading network.
1. Then, what does Tor do?
TOR, an acronym for The Onion Router, is free software that provides the users a chance to bring before them access to the Dark Web anonymously. Internet traffic is encrypted and routed that way through many nodes or servers making it very hard to trace user activity. The sites on the Dark Web use a .onion domain contrary to the supposed external .com or .org.
2. Getting into the Dark Web
Hence, the dark entities consist of:
Tor Browser- Best improved Firefox routing traffic through Tor. VPN- Virtual Private Network that ensures safety and confidentiality. Most websites have illegal and harmful content.
In most countries, visiting the Dark Web is not illegal, but visiting some websites and doing activities on these websites can be the cause for which a person would be found guilty in the law.
What Can You Find on the Dark Web?
It usually has been thought that the Dark Web is a very dangerous lawless desolation, but there are, however, some laws and rules that govern it.
Legal and Ethical Activities on the Dark Web.
1. Privacy and Anonymity:
The Dark Web allows communication between journalists and whistleblowers without risking surveillance.
Intelligent Distributing of Information Less-known encrypted messaging services are utilized by government bodies and NGOs.
Academia:
Some universities are studying cybercrime and digital forensics about the Dark Web
2. Illegal Activities on the Dark Web.
Not all activities in the Dark Web may qualify under illegal activities, but some would count as crime market places: A few of the most common illegal activities include:
- Selling Stolen Data- Hackers Sell in Competitor's Names.
Trafficking in narcotics: Were websites like the infamous Silk worth such an endeavor?
3.. Weapons Contraband
Some site offers illegal firearms and other contraband like fake IDs.
The cybercriminals have included hacking services offering malware and exploit kits.
The regular raids will thus be mounted because of these risks by law enforcement, such as the FBI and Interpol, on the walls of the dark web.
How To Be Safe Online:
Even not setting your foot on the Dark Web, you can always be affected by these cyber risks that usually hide in corners of the Internet. On these marketplaces, hackers still steal personal data and sell it; that is why every Internet user should have online security.
1. Use Strong Passwords and Passwords Unique to Each Account
Use strong passwords that must not be the same for different accounts.
Make use of password manager services (like Bitwarden, Last Pass) for saving and generating strong passwords.
Enable 2FA (two-factor authentication) for added protection.
2. Keep Your Software and Devices Up to Date
Regularly updating your operating system, antivirus software, and applications is very important because new security vulnerabilities may become discoverable. It is not advisable to use old unsupported software for this.
3. Be Careful of Phishing Attacks
Email users should be aware of phishing attacks. Warn users not to open hyperlinks or attachments in emails that seem suspicious. Properly validate the sender's email address before replying. If a user is uncertain about something, type the URL into the browser rather than clicking on a link.
4. Secure Your Internet Connection
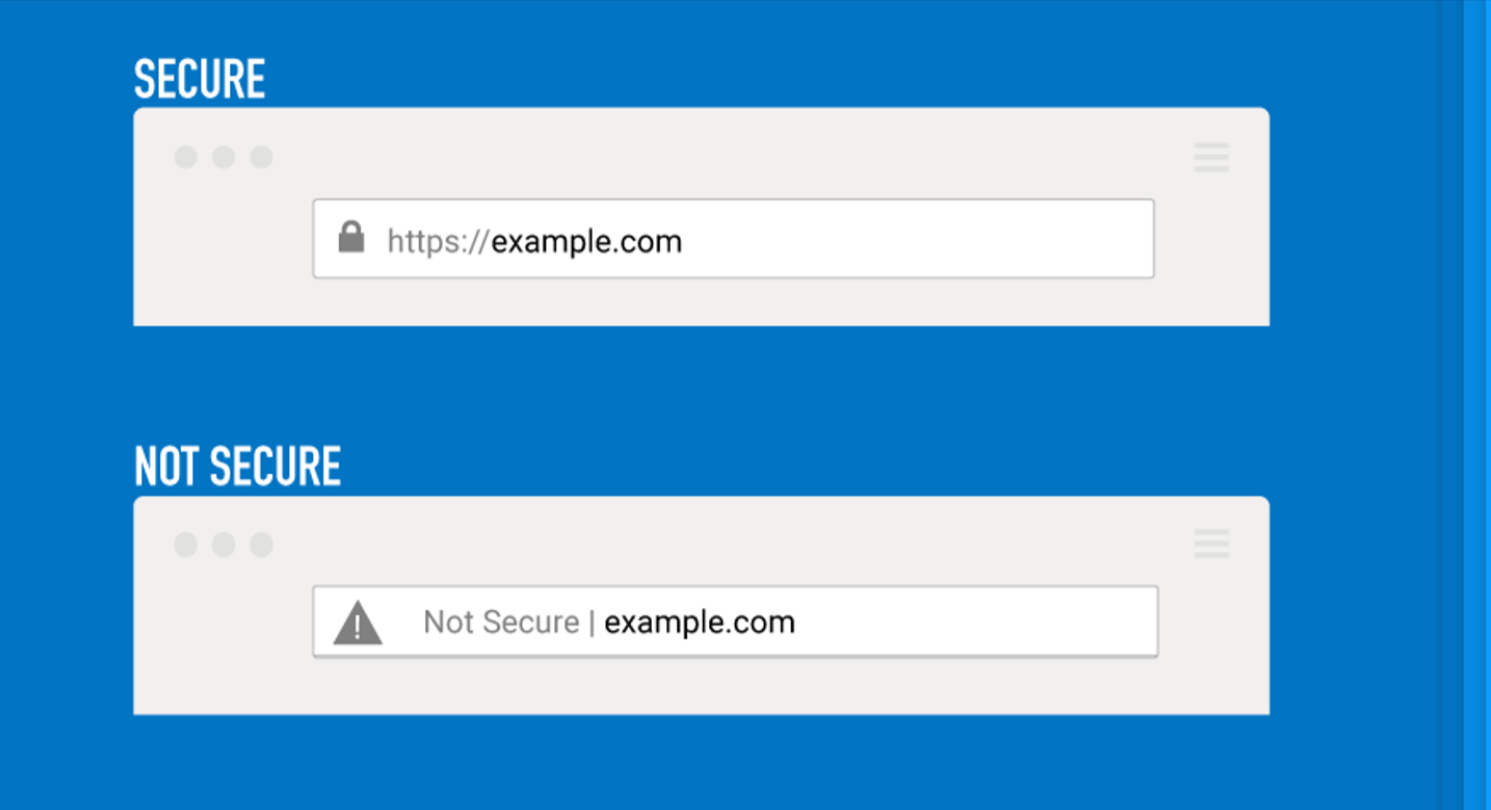
No Public Wi-Fi - Use a VPN (for example, NordVPN, ExpressVPN) when browsing online at the public place. Use HTTPS websites-http security institutions that use HTTPS encrypt data before transmission.
5. Monitor Personal Data
Check frequently with HIBP (Have I Been Pwned) regarding my email and passwords- to see if they were compromised. Set up monitoring alerts through identity protection services of personal information traveling in cyberspace.
6. Be Careful with Downloading Software
Download apps and software only from official sources such as Google Play Store and Apple App Store. Virus scan any download before it is installed.
Should You Ever Visit the Dark Web?
In fact, it is preferable to stay away from the Dark Web since there always seems to be some danger involved if you have no specific reason to enter this place. But others might have legitimate reasons to enter, being researchers, journalists, and cybersecurity professionals.
If you decide to explore the Dark Web:
Use a VPN - Adds an extra layer of anonymity.
Download nothing - Most Dark Web downloads are riddled with malware.
Never ever disclose - Protect your identity at all costs.
Stick to dependable sites - Some legit organizations such as ProPublica and SecureDrop have their Dark Web versions.
Remember that while there are things like Tor to safeguard one's identity, the law enforcement agencies heavily monitor and bust illegal activities on the Dark Web.
Conclusion
The Dark Web is one of the most misunderstood and talked about parts of the internet. The users who use this segment of the internet for their privacy have intended to provide a safe house for commodities and activities that lie under the canvas of being illegal. Anyone who is interested in online security should know the purposes and risks of the same.
Above all, it is also evident that even if you do not log onto the Dark Web, this layer still captures online threats that could have an impact on you. Use best practices such as installing strong passwords, enabling two-factor authentication, and beware of downloads-this will greatly help mitigate the occurrence of cyberattacks.